This post is for anyone using VPython to create animations. If you are having problems with lost/skipped frames when trying to capture the animations to video, here is a trick I’ve come up with to ensure every frame is reliably captured.
Continue readingReceive new posts by email:
-
Recent posts:
- Capturing smooth movies from VPython
- Reflections from the open end of a pipe
- How do wires work? (electromagnetic picture)
- The physics of toppling dominoes
- -1/12 and the area under the sum function
- The physics of a playground swing
- Kinetic energy of rotation around two axes
- The reverse sprinkler, part 3: results
- The reverse sprinkler, part 2: theory
- The reverse sprinkler, part 1: introduction
- Directly downwind faster than the wind
- Amplifiers in the real world: a case study
- Electromagnetic radiation from accelerating charges
- MEMS oscillator frequency increase from helium
- Android device encryption hang at Time remaining 00:00
- WebEx audio input hang on Linux (Chrome/Chromium bug)
- H field and material boundaries
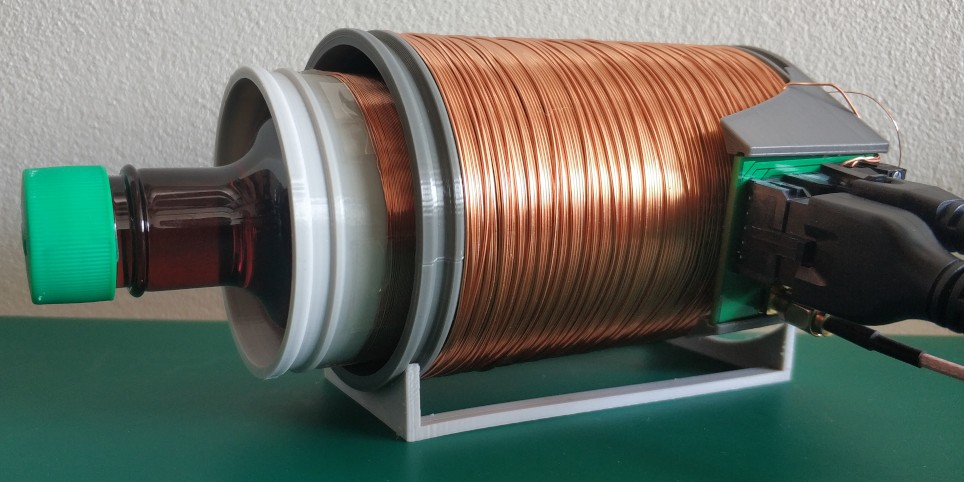
- Magnetic field of a ferrite core solenoid
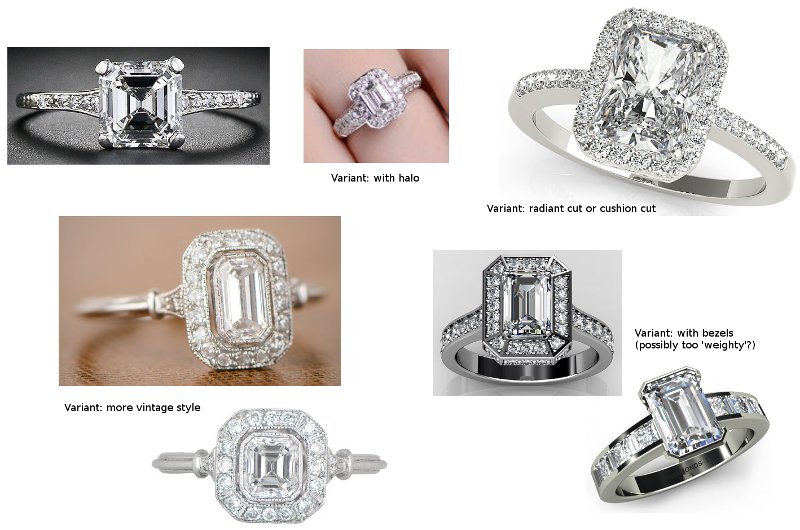
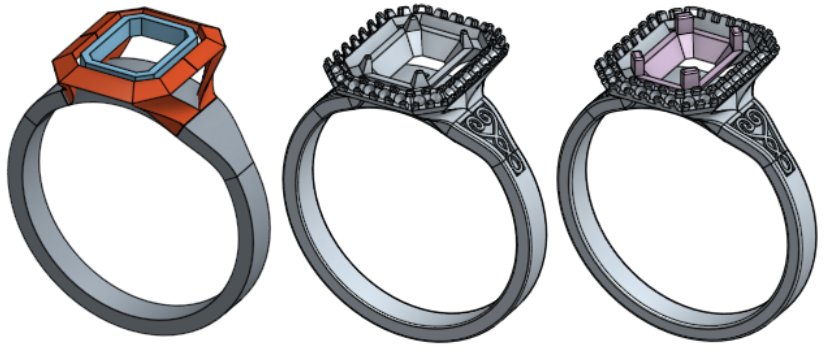
- Designing and making a ring
- Splines in Onshape, part 2
- Splines in Onshape, part 1
- Dell Venue 11 Pro travel keyboard troubleshooting
- Unlocking my Lenovo laptop, part 3
- Unlocking my Lenovo laptop, part 2
- Unlocking my Lenovo laptop, part 1
- Introduction to photography slides
- Global food security
- Weather balloon physics
- New site
Categories:

 BETA
BETA